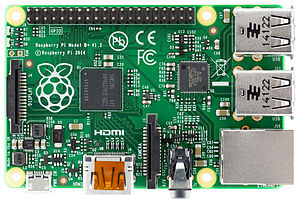
A few days ago I was checking my old hardware and I found a RASPBERRY PI (RPI) version 1 model B. It’s a very small computer module and this amazing hardware has two USB ports, 512MB of SDRAM, one Fast Ethernet (100 mpb/s), one HDMI, one RCA and a audio jack. In addition RPI requires an SD card to work as hard disk. It also has a small form factor measuring 65mm in length, it’s small as credit card and it works with a 5V/1.5A power supply. The processor is an ARM1176JZF-S with 700 MHz clock.
There are some operational systems available for this version of RPI, but I choose a version based in Debian called Raspbian, it is optimized for the Raspberry Pi hardware and it is supported by Raspberry PI Foundation.
I was learning about SAP Fiori frontend, as well as, I was developing an internal site at home in order to support some activities that I judge important for me. For example, sometimes I need to wake up some machine, monitor the surveillance cams and get alerts from nobreaks. Therefore I chose SAPUI5, because I could learn and enjoy my RPI at same time.
Recently I’ve started thinking about Internet of Things (IoT) and how to implement it at home. I’ve realized that Raspberry is a good choice for that kind of development, especially after the last announced version of RPI, the RASPBERRY PI ZERO, it’s smallest than RASPBERRY PI versions 1 and 2, and it’s cheapest than both.
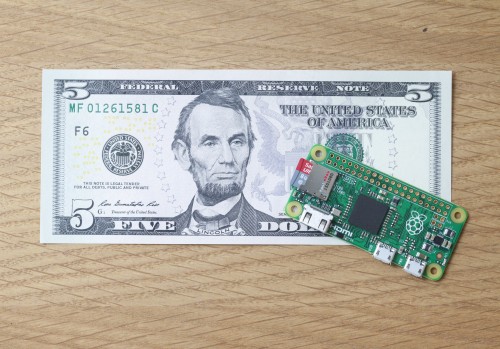
Raspberry PI ZERO Feautures:
- 1Ghz, Single-core CPU
- 512MB RAM
- Mini HDMI and USB On-The-Go ports
- Micro USB power
- HAT-compatible 40-pin header
- Composite video and reset headers
RPI Zero size
Lets take a look how to configure RPI to run OpenUI5 with Debian Jessie. If you are planning to use the Debian Wheezy keep in your mind that the configuration is a little bit different and probably you’ll experience some troubles.
- Preparation
Take a look here in order to install the RPI with Raspbian, it’s very simple and you can do it on Windows, Mac or Linux. Of course you need a SD Card.
The steps for configuration described below are for Debian Jessie and you can experience some troubles if you are trying to configure with Debian Wheezy installed on RPI. - Install and Apache Web Server
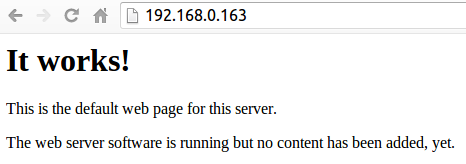
After you have installed your RPI, install the Apache Web Server. Do not forget, your RPI must be connect to the Internet by Cable or WI-FI.On the terminal type the following command:sudo apt-get install apache2 -y service apache2 restartTest your apache typing the url on the browser http://<RPI IP>. Example, if the RPI is running on IP 192.168.0.163, type http://192.168.0.163
You should see something like this:
- Deploy OpenUI5 on RPI
The root document configured for APACHE 2.4 is /var/www/html/Go to the web root and create the folder /ui5.Terminal commands:cd /var/www/html mkdir /var/www/html/ui5 cd ui5
Download the OpenUI5 sdk package
sudo wget https://openui5.hana.ondemand.com/downloads/openui5-sdk-1.32.9.zip

Unzip the package:sudo unzip openui5-sdk-1.32.9.zip
- Teste you environment
Go to browser and type the following URL http://<RPI IP>/ui5 in order to test your Openui5 SDK. Do not forget to REPLACE the <RPI IP>.
Example: http://192.168.0.163.
You must see a screen like this:
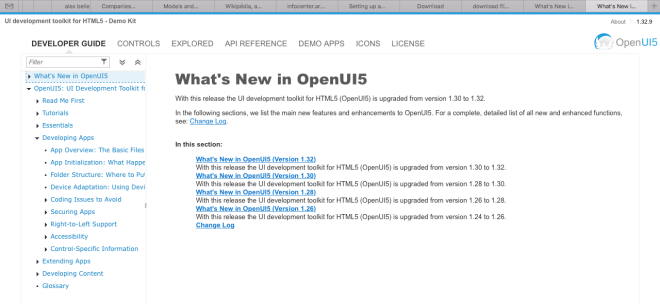
It is simple, isn’t it?
If you don’t have a RPI yet, you can test my configuration at https://www.zdecoder.com/ui5/
The same configuration can be applied for Ubuntu 14.04 with Apache 2.4.